UPDATE Post: 05/05/2020
The featured picture here is taken from an environment I worked on, where attackers had compromised a set of publicly available servers in Azure through a known vulnerability in Jenkins. Where the attackers got access to a public-facing VM and then using root access got access to the other servers in the same VNET and used it for bitcoin mining.
Lately, there have been increased ransomware attacks, where companies are faced with their systems and data becoming encrypted and forcing them to pay a ransom to get access back to their data. A couple of weeks ago I started to subscribe to https://shadowintelligence.io/ feed just to see how many companies are getting affected (and I’m guessing this feed is just showing the tip of the iceberg) I get multiple emails each day, informing me about new businesses that are being affected by ransomware.

Also seen that there have been some targeted attacks against Norwegian Parliament as well https://www.zdnet.com/article/norwegian-parliament-discloses-cyber-attack-on-internal-email-system/ while we don’t know how the attackers gained access, we know some of the gateways such as Office 365, ADFS, BIG-IP is in use there.
And even in Finland now where an attacker gained access to an Eletronic Patient record (EPR) where they are holding Psychotherapy Data Ransom. where the data contained 40,000 therapy patients, many under age, is demanding €200 from each patient. The EPR system was running an outddated version of Ubuntu 16.04.1, Apache 2.4.18 (Which came out in 2015) and PHP 5.6.40, which all contain many known vulnerabilities. (Information can be viewed here –> https://www.shodan.io/host/95.175.109.219 )
Last week one of the largest consulting firms in Europe was also hacked using a new variant of Ryuk. Ryuk attacks have also recentlty adoptied to exploited the vulnerability ZeroLogon as well.

Source: https://thedfirreport.com/2020/10/18/ryuk-in-5-hours/
This gives an deeper understanding on how they operate and what kind of tooling that is used to gain access. Where the attackers in four hours and 10 minutes in, the threat actors used the pivot from the primary domain controller to RDP into the Backup server. This is also the similiar pattern that Microsoft described in their Digital Defender Report from September 2020 https://www.microsoft.com/en-us/download/confirmation.aspx?id=101738

Now looking in the attack patterns the different threat actors are using, it is a mix of the different examples described underneath here. This just highlights some of the ways that attackers can get access to an environment.
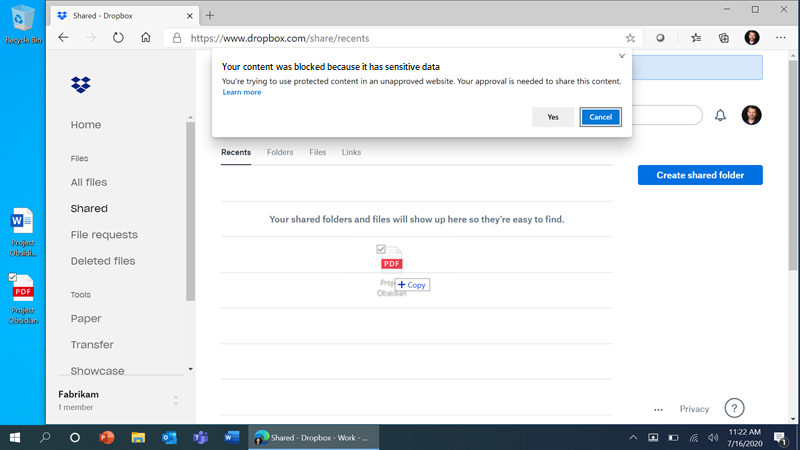
However the attackers are also now changing tactics and going from where they just encrypted data to now extracting data and holding the data outside of customer infrastructure to ensure that the ransom is paid. Then holding a reverse auction to allow the customer to get access to the data again. This means that protection of data and “assume breach” are more important than ever.

Lastly, we also see more DDoS based attacks and with the introduction of new protocols such as QUIC which is aimed at providing a faster browsing experience will also put more businesses at risk of DDoS based ransomware attacks, which we have also seen more and more attacks happening.

1: Exploiting known vulnerabilities to get access to the corporate network, such as exploiting vulnerabilities in remote access services (Looking at the vulnerabilities that have been with Pulse VPN, F5, Citrix NetScaler, Fortinet) and such it is a pretty long list. If attacks were able to utilize one of these they could get access to the inside of the corporate network. Also many of these providers also provide load balancing services and such and therefore be easy for attackers to manipulate load balancing services and expose them directly to the internet. Or that you have systems that are accessable from internet directly such as RDP or exposed web services running an outdated version of a web-engine or OS.

2: Access through credential stuffing. This is where attackers are leveraging legitimate accounts to get access to the corporate network. This happens because user account information has been hacked, for instance if a user has used the same username and password for other 3.party websites and those sites get hacked. As an example of this, last week Norway Parliament was hacked through E-mail. How the attackers got access is still not known but looking at some of the representatives on the Norwegian Parliament on haveibeenpwnd.com showed that they like to reuse their account information for other 3.party websites as well.

3: Access trough brute-force attacks. What we have also seen from others is that attackers are performing password spray attacks, which are either going against Office 365 directly where they try to authenticate using legacy protocols which does not have the same protection mechanisms like the other authentication options in M365. Then a user login log might look something like this.

Microsoft is fortunately removing support for Legacy authentication protocols which will also limit the ability to do these password spray attacks. A Similiar attack vector to do password spray attacks can also be done against ADFS (Active Directory Federation Services) and especially if you are running an older version of ADFS such as 2012. With the newer additions of ADFS you have new features such as integation with Azure MFA.
4: Access trough compromised workstation or end-user machine. This can happen through a phishing email where the attackers lure a user to visit a website and download a payload or trough an attachment in an email. This can be trough an email from a spoofed domain to appear to be an email from a colleague or a legitimate business. Also, when looking at phising as the data shows, most kits have a short life, and the window of opportunity for most phishing kits is growing smaller. In fact, over a 60-day period, Akamai observed more than 2,064,053,300 unique domains commonly associated with malicious activity. Of those, 89% had a lifespan of less than 24 hours, and 94% had a lifespan of less than three days. Making it extremely difficult to block using traditional DNS protection services.

Now once a threat actor gets access their approach differs. Some ransomware is just intended to spread and infect files that are available from the infected resources. Some threat actors will try to do lateral movement and try to gain elevated access to be able to 1: Infect as much as possible – Utilizing such as Domain Admins to infect all infrastructure and workstation within the domain, 2: Steal corporate data which they then upload somewhere and auction the data or hold the business “hostage”. Threat Actors that want to get higher level of privilege using different lateral movement techniques and tools to move around in the environment and in the end try to get access to a domain admin account.

Another issue that many companies have been facing when their systems got compromised and data was encrypted, was that their backup software also get impacted, which means that backup data was also encrypted.
So how can we protect our business completely from these kinds of attacks? First of it is important to map your environment and understand where those initial attack vectors are and determine the risk. Therefore, I decided to split it into different sections and describe ways to reduce the attack surface and reduce the risk for ransomware in your environment.
Countermeasures
1: Credential Stuffing
This is a brute-force attack technique, but instead of trying to guess passwords using “dictionaries” of common word combinations, attackers use lists of known valid credentials obtained from data breaches. As a company there are some tools and services that you can use to determine if user credentials have gotten compromised. 1: Is trough Azure AD Identity Protection, if you are using Azure AD as your main authentication service 2: Subscribe to haveibeenpwnd.com using domain search 3: Other tools like F-Secure Identity protection https://www.f-secure.com/en/home/free-tools/identity-theft-checker
Again to prevent future compromised credentials on 3.party websites, this is all about educating users about the risk of reusing usernames and password on other websites. Now regardless if we educate our end-users there will always be someone that forgets, so it is important that we have proper monitoring and logging in place to determine WHO / WHAT / WHERE / WHEN someone logged into our services. An example or monitoring tools that can be useful here is Azure Log Analytics which can be used to collect security events related to Active Directory and other services using other log formats such as Syslog.
Also important that you have properly configured Group Policy to ensure that important activities are logged into the security logs according to the baseline defined here –> https://docs.microsoft.com/en-us/windows-server/identity/ad-ds/plan/security-best-practices/audit-policy-recommendations (as part of Stronger Recommendation policy)
Using Log Analytics you can then see when someone logged in, and if combined with Azure Sentinel you can also provide ML to determine abnormal user behaviour to logon processes to services such as running RDP (https://docs.microsoft.com/en-us/azure/sentinel/connect-windows-security-events)
Here is also an list of different hunting queries that can be used together with collected logs (https://github.com/Azure/Azure-Sentinel/tree/master/Hunting%20Queries/SecurityEvent)
Against Active Directory, Microsoft also has a specific product called Azure Advanced Threat Protection which monitors and analyzes user activities and information across your network, such as permissions and group membership, creating a behavioral baseline for each user. This is not an replacement for traditional logging but is useful to detect certain attacks and lateral movement inside your domian.
2: Brute Force Attacks / Password Spray Attacks
When it comes to brute-force attacks or password spray attacks. This is determined on what kind of services the attackers are trying to brute force, therefore I listed some of the identity solutions / services and lists some of the protection mechanisms that you can use.
- ADFS: Many organizations have been affected by password spray attacks, where they had an outdated version of ADFS configured which was not enabled with any type of MFA solution, and therefore open to password spray attacks. Attacks are also often trying a range of usernames and therefore makes it difficult to block specific users. The best approach is to 1: Enabled extranet smart lockout feature (https://support.microsoft.com/en-us/help/4096478/extranet-smart-lockout-feature-in-windows-server-2016) and integrate with Azure MFA using the native integration https://docs.microsoft.com/en-us/windows-server/identity/ad-fs/operations/configure-ad-fs-and-azure-mfa
- Azure AD / Office 365: Within Office 365 the biggest attack vector with password spray attacks are attacks trough the legacy authentication protocols, disabling these protocols will make it difficult for attackers to do password spray attacks (https://docs.microsoft.com/en-us/azure/active-directory/conditional-access/block-legacy-authentication)
- Other SaaS services: For other Web applications and services, it is important that you as a company try to standardize on a single iDP for your end-users. If you are using third party SaaS services, look to integrate those with Azure AD to provide a centralized idp solution. Secondly if supported collect logs and activity monitor logon attempts to those as well, some SaaS services support integration against Microsoft Cloud App Security to monitor abnormal behaviour.
- Web Applications: When you have public facing web applications, they can also become a target for attackers which they try to get access to. If you have load balancers in front of these services, many of them have HTTP DoS protection features which can be used to present a JS challenge to determine if the attacks are coming from a legitimate client. Again look at others ways that these services can be exposed, trough services such as Azure Active Directory Application Proxy, where services are behind Azure AD Identity services. Regardless on which type of web server it is running, it is important that http logs are also collected and analyzed by a centralized log system to determine usage of the service. If you are using NGINX for instance, you can also implement rate limiting to slow down requests, https://bobcares.com/blog/nginx-brute-force-protection/ or have IP reputation features that can also block requests from “known” IP addresses.
- VPN / Remote Access solutions: An important part is that providing a VPN or remote access solution is having again a centralized identity service. If you are already using Azure AD for MFA services, then look to implement the same MFA solution against the remote access or VPN service which can be done using the NPS Extension to provide a RADIUS integration against the VPN provider https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-nps-extension-vpn or an better solution is if the remote access solution supports SAML and can be directly integrated against Azure AD.
- RDP: If you need to have RDP exposed you should investigate if you could replace it with another service such as Azure Bastion, JIT services or proxy services which are available.
Regardless of services that you have the most important aspect is making sure that services have logging enabled so that you have visibility into what is going on.
3: Exploiting Vulnerabilities
Protection against vulnerabilities are pretty simple but yet difficult, patching. This may sound simple, but most companies struggle since their environment is complex and lacking the visibility to see the threat landscape and having the resources to follow this up. There have been many companies that got compromised because of an unpatched Pulse VPN software 6 months after the vulnerability became known, same has been the issue with Microsoft Exchange where there was a big vulnerability https://healthitsecurity.com/news/82-of-vulnerable-microsoft-exchange-servers-remain-unpatched. This means that organizations need to do one of two things.
- 1: Follow the current threat landscape and looking at the trends based upon services that are deployed inside the company, then patch when new vulnerabilities emerge
- 2: Outsource services, to a cloud service or to a trusted partner. Now the issue that many companies are struggling with is resource/expertise to handle this on their own. Using a cloud service as an alternative can be an option or that you use a service provider.
- 3: Having a threat and vulnerability scanning solution which can also provide insight into current threats to be able to easier see vulnerabilities in your organization. As an example, here Microsoft provides with Security Center which can do threat detection on infrastructure and services, also together with Qualys provide application-based vulnerability scanning.
4: Compromised endpoint
Now since most infections and cyberattacks starts with an email it is important that you have predefined security in place in your email service to block as much phishing email as possible and remove spoofed email from internal domains and have scanning of attachments and URL’s in links to ensure that users are not tricked into running some form of payload on their endpoint.
Now there are a couple of things that need to be part of this security chain.
- 1: Email based security:
Here there are different security mechanisms that needs to be in place to reduce the amount of spam mail, such as looking into the DNS security. This is where some core DNS specifications to DMARC, DKIM and SPF which provides the following. Put simply, SPF, DKIM and DMARC are ways to authenticate your mail server and to prove to ISPs, mail services and other receiving mail servers that senders are truly authorized to send email. When properly set up, all three prove that the sender is legitimate, that their identity has not been compromised and that they’re not sending email on behalf of someone else. These features can limit the use of spoffed emails looking to orginate from within your own organization and can therefore also limit the use of phising attacks. There is also an guide which showcases a lot of the security best-pratices for Office 365 and the surrounding ecosystem (https://query.prod.cms.rt.microsoft.com/cms/api/am/binary/RE2MHP5)
Office 365 also has many different security mechanisms that can be used to decect and block email containing malicious attachments and malicious URL’s. These services are part of Office 365 ATP https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/office-365-atp?view=o365-worldwide
They also have anti-phising features which uses Machine Learning to detect abnormal behaviour https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/set-up-anti-phishing-policies?view=o365-worldwide#exclusive-settings-in-atp-anti-phishing-policies
- 2: Endpoint based security
If the attackers managed to send an email which has bypassed all the traditional email security features then the next part is having features in place to ensure that the endpoint doesn’t execute the payload or be able to block the content.
The first aspect is having a client which is running anti-malware and EDR solution to be able to see process/files/registry changes and activity on the machines and also be able to block against threats either based upon signatures or other sandbox detection mechanisms. In many cases, new malware and payloads doesn’t need a lot of permissions or is a new variant and therefore undetected by many anti-malware providers which also means we need more layers of security. To showcase some of the features which can be used to provide protection in the different layers.
* Application Guard ( Which is now available for Browsing and Office –> https://support.microsoft.com/en-ie/office/application-guard-for-office-9e0fb9c2-ffad-43bf-8ba3-78f785fdba46 ) runs content in a locked down VM container which prohibits communication with host OS.
* Restricting PowerShell and logging activity –> https://www.digitalshadows.com/blog-and-research/powershell-security-best-practices/
* Removing older versions of PowerShell and enabling Logging of PowerShell Commands
* Having an EDR system installed that can monitoring activities
* Locking down using Baseline configuration. You can for instance using CIS Benchmark as a way to lock down and provide security best pratices for Windows. https://www.cisecurity.org/benchmark/microsoft_windows_server/
Some other countermeasures are
- Deactivate running of Office Macroes (Group Policy)
- Change default file behaviour for HTA/JS/JSE files using Group Policy
- Add External Warning Header in Email. Meaning that all external email will automatically apply a header saying it is external
- Apply latest version of Microsoft Edge to provide built-in Password Monitoring
- 3: Monitoring and logging
Now regardless of which service you are using for email, it is important to have proper logging in place to ensure you have visibility into email traffic and also see what is going on from an endpoint perspective. A lot of the ransomware payload today which is running on the endpoint which can start as an simple excel sheet or word document with a macro or a executable which runs a powershell script and psexec command to download more payload or communicate with other resources on the same network.
Office 365 provides an extensive logging features which can be enabled (not enabled by default): https://docs.microsoft.com/en-us/microsoft-365/compliance/search-the-audit-log-in-security-and-compliance?view=o365-worldwide and can also be forwarded to Log Analytics or Azure Sentinel to provide a centralized log management service. This in conjunction with an EDR tool to map events against processes and file changes and network communication to detect abnormal traffic or behaviour.
This list also highlights some of the different log sources that should be collected to be able to monitor for abnormal behaviour in a windows based environment –> https://www.cyber.gov.au/sites/default/files/2019-10/PROTECT%20-%20Windows%20Event%20Logging%20and%20Forwarding%20%28April%202019%29.pdf
- 4: Design to reduce infection to other parts of the infrastructure
So what if your endpoint is compromised and the attackers have managed to bypass all the security mechanisms that are part of your security platform? Historically endpoints have been bart of Active Directory and been one happy family. Which presents a problem, this means if that someone managed to compromise an account/device which has elevated level of access it will also automatically spread to other part of the infrastructure the users have access to.
From there they can also use a range of different tools and techniques to do lateral movement, climbing further up in the infrastructure and trying to get higher level of access to systems. The end goal? to be able to infect/distribute their ransomware to as many end-users/devices as possible. Such as the operators behind the MAZE ransomware use a combination of tools such as Bloodhound and PingCastle to map and understand customers Active Directory structure. They also often leverage tools such as Procdump and Mimikatz to collect end-users’ credentials for a later stage attack.
Once the attackers get high-level access to a set of privileged user accounts, they strike. Using a combination of different built-in functionality and tools to propagate the ransomware. The attackers often use tools and built-in features like
- Group Policy
- Administrative shares, Network Shares
- Microsoft PsExec tool
- WMI, SMB or other remote tooling to deploy the payload/executable
- They have also been known to leverage unpatched exploitation methods (e.g., Eternal Blue – addressed via Microsoft Security Bulletin MS17-010).
Countermeasures to apply to reduce the risk
- Disable older versions of SMB protocol
- Ensure SMB Signing is enabled

- Upgrade to newer versions of PowerShell and remove older versions
- Collect log data from Windows Event Log “PowerShell Operational”
- Install Windows LAPS (Free) Download Local Administrator Password Solution (LAPS) from Official Microsoft Download Center
- Use Group Policy to deny access to this computer through remote desktop services Group policy
- Ensure that you have adequate logging for infrastructure, use this list as a recommendation –>
- Use Sysmon to collect process monitoring if not other monitoring capabilities are available
- Monitoring DNS traffic for queries to malicious domains can be done using Log Analytics and DNS monitoring (or Sentinel)
- Block Traffic to and from Tor Addresses using some form of IP reputation or DNS filtering (pref both) and NDR (Newly Created Domain Records)
- External Services should be monitoring for known vulnerabilities.
Which they then use to distribute the ransomware across clients, servers, and data in the organization to infect as much as possible.
Much of the technique they use to distribute their ransomware is possible because of the way Active Directory is configured and has historically operated, where end-users and devices have been part of a large trust-based architecture. Which means that if you are on the inside you can based upon the architecture get access and SSO to resources if you have access.
One way around this is building an architecture using Azure Active Directory.
Moving end-users and devices to an Azure AD based management, means that devices are no longer part of the Active Directory domain. Much of the innovation and development that Microsoft is now doing is within the Windows 10 and the ecosystem. Also seeing that moving forward Azure AD will be centralized management service as will replace Active Directory.
Moving devices to Azure Active Directory means that we can use conditions to determine if a user/device should get access to data and applications. Looking back an example with an infected device, we can with Azure Active Directory have Conditional Access Policies which are then used to determine the health of the device and user to ensure that there is no risk before they are allowed access to the data. With the machines being Azure AD based, it means that attackers cannot directly leverage lateral movement techniques against admin shares and network drives using regular SMB protocols or tooling like Group Policy.
Azure Active Directory also collects health/risk information from multiple sources to determine the risk of the user and the device the user is coming from, such as Defender ATP, Azure ATP, and Microsoft Intune. These in turn can be used to determine if the user or device are allowed to access data or an application.
Another part to reducing the impact of ransomware attacks, is that data should be moved away from traditional file servers to a type of cloud-based storage solution such as OneDrive For Business where you have versioning capabilities, there are few ransomware attacks that affects cloud-based storage from an end-user client. Secondly storage services which are integrated with Azure AD means that we can have the same security mechanisms in-front of storage services as well.
5: Protecting backup services
If we manage to move to a full Azure AD based management for our end-users and clients, many servers and applications might still be dependant of Active Directory. Therefore, it is also still important if you want to protect against ransomware attacks that you
- Have an Active Directory disconnected backup solution (reduces risk for lateral movement) and encrypting backup services.
- Have an offline backup (reduced the risk that backup data is also encrypted)
- Back up important files regularly. Use the 3-2-1 rule. Keep three backups of your data, on two different storage types, and at least one backup offsite. This can be easily done using Cloud based backup solution as an cheap offsite backup option, such as Azure Backup or Veeam Backup.
- Verify backup data integrity and that you have a Disaster Recovery plan.
- Also there are different features in M365 and Windows 10 you can use to reduce the risk of ransomware attacks or the effect it has –> https://docs.microsoft.com/en-us/microsoft-365/security/office-365-security/recover-from-ransomware?view=o365-worldwide
The most important part is educating the users so they can identify social engineering and spear-phishing attacks. Since the initial compromise often happens through email or malicious websites. A good indication of checking if a website or domain is part of ransomware or phishing attack you can use
https://www.virustotal.com/gui/
6: Encrypt your data
To ensure that your business will not be held for ransom, ensure that you data is encrypted at real-time as well. You have tools such as Azure Information Encryption and other features which can be used to encrypt data to ensure that if attackers gain access to it that they are not able to use it for ransom. This of course is not applicable for all types of data, but to ensure that data is not directly readable. This is also something that Microsoft is pushing and providing new capabilities as part of Endpoint DLP.
Final advice
Now the final advice I want to give, it is important to understand the current threat landscape that we are currently facing. With new big vulnerabilities being discovered on a weekly basis it is important to understand the consequences if you do not patch as soon as possible to reduce the vulnerability. If you do not have the capacity to ensure lifecycle management of these products you are using, get a partner or someone to provide managed services to ensure that the security is maintained. Also map your current environment ensure that you don’t have any exposed services and if so, determine the risk and apply any countermeasures that you might apply.