When Windows 11 was announced, Microsoft made a huge change to its hardware requirements which was they will now require TPM 2.0 compatible chips on your machine to be able to run Windows 11.
TPM today is required for a lot of other services in Windows like
- BitLocker Drive Encryption
- Windows Hello PINs and biometrics
- Windows Defender System Guard
- Tamper detection of the PCs hardware
- Virtual Smart card
- Credential Guard
- Secure Boot
The last feature is one of the reasons why TPM will be mandatory, to be able to use Secure Boot in Windows 11 which is enabled by default. When the PC starts, the firmware checks the signature of each piece of boot software, including UEFI firmware drivers (also known as Option ROMs), EFI applications, and the operating system. If the signatures are valid, the PC boots and the firmware gives control to the operating system.
Secure Boot process
Secure Boot was made to help make sure that a device boots using only software that is trusted by the OEM.
When a PC starts, it first finds the operating system bootloader. PCs without Secure Boot simply run whatever bootloader is present on the PC’s hard drive.
When a PC equipped with UEFI starts, the PC first verifies that the firmware is digitally signed, reducing the risk of firmware rootkits. If Secure Boot is enabled, the firmware examines the bootloader’s digital signature to verify that it hasn’t been modified. If the bootloader is intact, the firmware starts the bootloader only if one of the following conditions is true:
- The bootloader was signed using a trusted certificate. In the case of PCs certified for Windows 11.
- The user has manually approved the bootloader’s digital signature. This allows the user to load non-Microsoft operating systems.

So many started asking do I really need TPM 2.0 to install Windows 11? The answer is no… You can bypass the requirement
1: During installation press Shift+F10, open registry and create key LabConfig under HKEY_LOCAL_MACHINE\SYSTEM\Setup There add: “BypassTPMCheck”=dword:00000001 “BypassSecureBootCheck”=dword:00000001
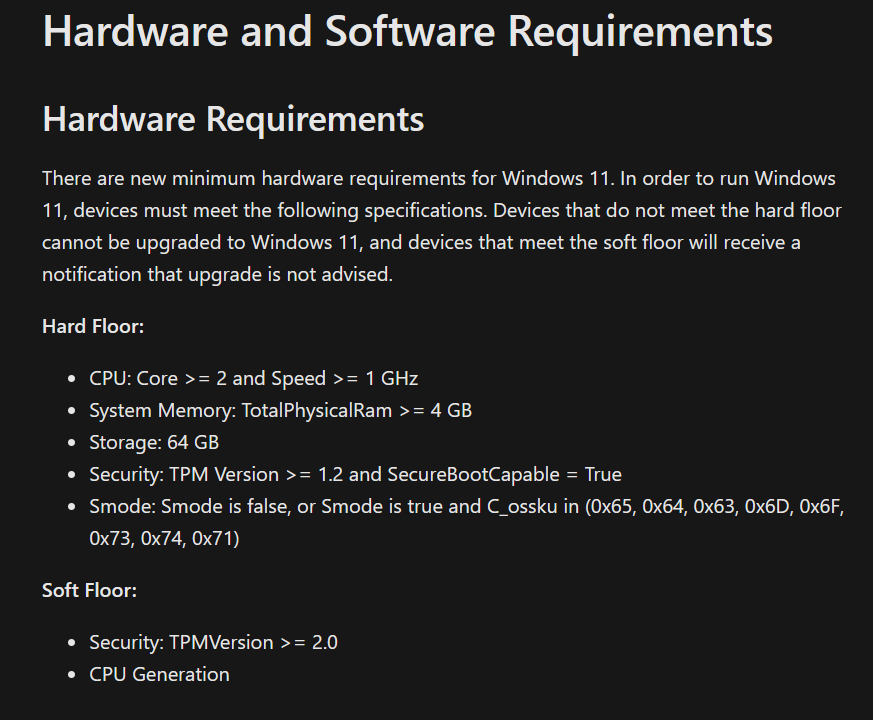
2: Secondly the hard requirement is actually TPM 1.2. Devices that do not meet the hardware requirements cannot be upgraded to Windows 11, and devices that meet the soft floor (aka TPM 1.2) will receive a notification that upgrade is not advised.”
So why is TPM 1.2 not advised anymore? You can read the differences between v 1.2 and v 2.0 here –> TPM recommendations (Windows 10) – Microsoft 365 Security | Microsoft Docs
What if I cannot upgrade to Windows 11, what are my options? Microsoft will continue to support Windows 10 through October 14, 2025.
How can I check if my machine has TPM?
There are multiple ways to check.
1: PowerShell (Get-TPM)
2: CMD (tpmtool.exe getdeviceinformation)
3: MMC (TPM Snap-in) (This shows that TPM is not present)

4: Windows 11 Health App PC (Which is an app developed by Microsoft to check for upgrade readiness for Windows 11) that you can download here –> https://aka.ms/GetPCHealthCheckApp

How will this be for Cloud-based desktops?
With the requirement for TPM present, how will this then work for Cloud-based deployments? This means that Windows 11 machines (most likely) need to be deployed in an environment that supports vTPM.
For Azure-based deployments, this means that as of now you need to use Trusted Launch for virtual machines.
It should be noted that this feature is in public preview also is only available in certain regions and certain VM SKU’s
- B-series
- Dav4-series, Dasv4-series
- DCsv2-series
- Dv4-series, Dsv4-series, Dsv3-series, Dsv2-series
- Ddv4-series, Ddsv4-series
- Fsv2-series
- Eav4-series, Easv4-series
- Ev4-series, Esv4-series, Esv3-series
- Edv4-series, Edsv4-series
- Lsv2-series
And currently available in these regions
Regions:
- Central US
- East US 2
- South Central US
- North Europe
- West Europe
With Trusted Launch, it also introduces vTPM for Azure VMs. This is a virtualized version of the hardware Trusted Platform Module, compliant with the TPM2.0 spec.
Here is an example of a VM in Azure running Trusted Launch with vTPM

To deploy a VM in Azure using Trusted Launch and vTPM you need to create new VM’s is it not supported on existing VM’s. You can use this unique URL to enable the trusted launch options in the UI
Then when creating a virtual machine, you will need to choose generation 2 virtual machines in the image options

Then choose to enable vTPM under the advanced page.

What else is new?
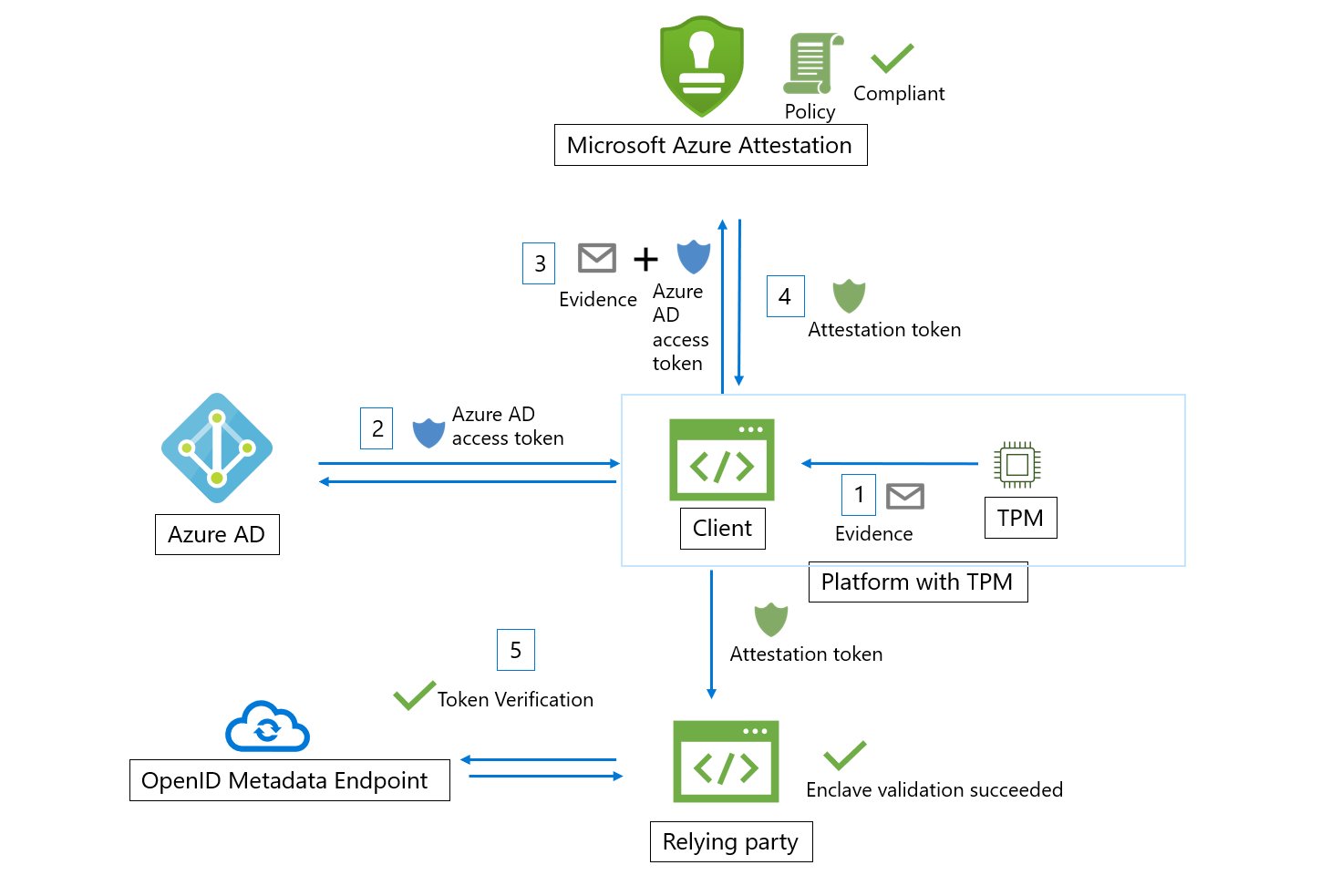
What thing that is not that known is that Windows 11 will have native integration with Azure attestation services. That will allow us to verify the identity and security posture of a client before we give it access to services.
This means that for instance, a Windows 11 machine together with TPM and Secure Boot can notify Azure AD about the security configuration on the machine, which can be generated into an attestation token before giving the endpoint access to the application/data/services. Still remains to see how this works in practice.