So I decided to try the ARP guard functionality in Hyper-V 2012 and see how it works, and in the same case check if it is possible to change the Mac address.
I took a look at what documentation Microsoft had around the subject
http://blogs.technet.com/b/wincat/archive/2012/11/18/arp-spoofing-prevention-in-windows-server-2012-hyper-v.aspx
http://technet.microsoft.com/en-us/library/hh831823.aspx
And what they say here is that
I am sure you already browsed the new Hyper-V Manager UI and found a couple of new settings like DHCP Guard, Router Guard but nothing specific for ARP Spoofing.
Well, the feature you are looking for is called Port Access Control Lists and is implemented in the new Hyper-V switch and must be configured via PowerShell.
Arp Spoofing is a technique that allows for man-in-the-middle attack.
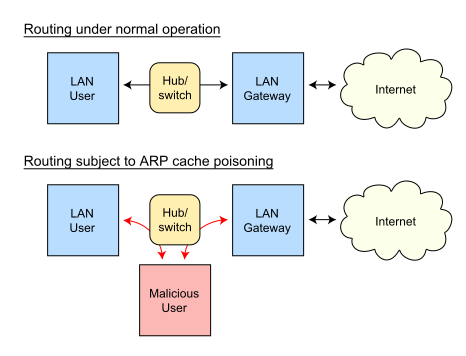
I can for instance place my computer in the middle of another user and intercept all the traffic going between the end-user and the gateway and place a sniffer on my computer and scan all the traffic going in and out.
Without the user even knowing it. This can happen because of how the Arp protocol is built. It is built on trust, and how computers can find other computers on the same subnet and was never thought of as a secure protocol.
So in order to test this out I had to setup a minor lab built with a couple of VM’s running on a hyper-v 2012 virtual switch.
1: with Windows Server 2008 R2
1: one domain controller
1: Linux Backtrack (which I will use arp spoof and mac changer on)
So when I start my newly installed WS2008 server It has a clean arp table (which consists of the broadcast address)

And as you can see this computer has the IP address 10.0.0.56
So what happens when I ping this server from the backtrack computer ? First the arp request (who owns this ip ? )

You can see the arp request first, then the ICMP protocol start. Then the Arp table is updated.

As an dynamic update. Then I ping the domain controller, which has ip 10.0.0.1,

and it has added itself to the list, look at difference between the mac addresses of 1 and 77.
Next I start the arp-spoof attack from my backtrack computer.
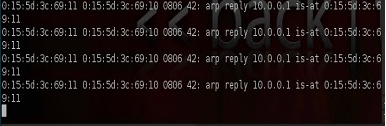
And I can see in wireshark that I am spamming with ARP traffic

And notice here I am saying that IP 10.0.0.1 is at another MAC address.
If you check the arp table now on the other computer you can see that the arp table is updated (poisoned)
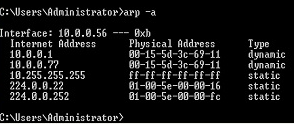
And after I activate IP forwarding on the backtrack server I can “act” as a man in the middle.
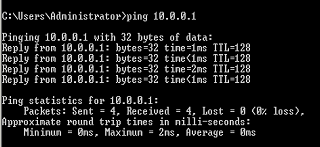
As you can see now when I try to ping 10.0.0.1 I get a response

but from my Backtrack server instead of my domain controller. And according to my server it responds fine from 10.0.0.1
So how does the arpguard in Windows Server fit in here? In addition, where can I configure it?
The answer is Port Access Control Lists via PowerShell.
This is configured on the Hyper-V host I find it a best to do it via the PowerShell ISE.
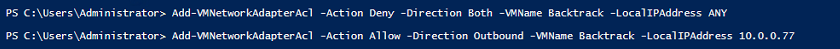
so what can I do ? First, I have to create a port ACL that defines that the virtual machine can ONLY communicate out with the IP address of 10.0.0.77 and not any other.
So when I apply this port ACL and try to ping 10.0.0.1 It will not receive a response, and since it does not get a response I tries an ARP request again and my backtrack computer is unable to respons because of the Port ACL

And the arp table is restored to its default.
