As part of the new Microsoft Enterprise Mobility + Security E5 or as a standalone product, Cloud App Security is a new product which deliveres alot of cool functionality. Up until now, alot of the products in the EMS space have been aimed at controlling the endpoints (Intune) , controlling and protecting the data (Azure information protection), and protecting the user (Azure AD) and with Cloud App Security, it is more of controlling the data flow and getting if users are violating rules and creating alerts if they for instance are sharing data with the competitors for instance. Another example might just be that an user clicked wrong and shared data with ALL external resources for instance. (Here is the list of supported Cloud Appilcations and API’s https://docs.microsoft.com/nb-no/cloud-app-security/enable-instant-visibility-protection-and-governance-actions-for-your-apps)

Now it can integrate directly to different cloud applications using connectors which leverages the apps API’s to search and identify risks. Now in most cases that might not be enough, for instance an application might not have opened their APIs to dig down into the material, but Cloud app Security can also use uploaded traffic logs from on-premises proxies and firewalls like Palo Alto, Cisco, Forefront and such and also hypervisor, which allows it to collect larger amounts of data and digest it ( Here is a list of supported network devices –> https://docs.microsoft.com/nb-no/cloud-app-security/set-up-cloud-discovery )

Now I didn’t have any firewalls I could do log shipping from so I just used the built in app connector to Offiec365 to see how it worked. First I setup a connection with Office365 and the other applications which was pretty easy since I already had a Office365 tenant with my account
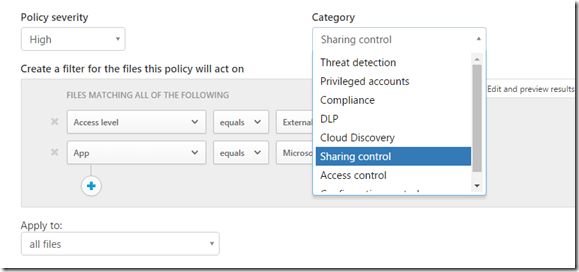
So now I wanted to create a policy which showed if some users were sharing any files/folders from OneDrive for Buisness with competitors or excluded domains for instance, so I went into Control –> Policies
From there I choose to create new policy based upon file policy.
I choose a default template which is aimed at sharing data with uauthorized domain
So here I specify which app this policy is going to be aimed at which is OneDrive for Buisness.
Now moving down the policy I can also, specify the policy to do content inspection on the files, to search for some specific content in the files.
I hate regex, but they ahve given some good example here how to use the filter policy part –> https://docs.microsoft.com/nb-no/cloud-app-security/working-with-the-regex-engine I can also specify governance rules, which allows me for instance to do automatic quarantine of the user which has done this for instance
But I just leave it at default and click Create. Now If I go back to the dashboard I can see that I have an alert being triggered after it has scanned the Office365 shares.
Bingo! “Recent Alerts: File Shared with unauthorized domain” now it was triggered because I have a one drive where I’ve shared something with an external user
Now I have some pretty advanced features I can do directly from the alerting pane
To for instance put the user in quarantine, remove the collaborator or look at the users activities for instance, but this is just an example of policy uses. For instance I can also create a policy which looks for suspicious activity based upon where the users on from (ISP, Country) for instance. There are also some other nifty built-in policies
Now this product covers most of the used SaaS applications, but I feel like this should be baked into AzureAD and also given some more details around other SaaS applications, also maybe have the option to include Azure AD cloud app discovery as part of this as well?