So this is based upon a session I had at Hackcon a couple of weeks back. There are more and more businesses moving or adopting public cloud one way or another, it can be SaaS, PaaS or traditional IaaS features to move their existing datacenter to the cloud. Now if we look at the cloud market today 5 vendors make up over 50% of the total market for public cloud where the vendors are (Amazon, Google, Microsoft, Salesforce and IBM) So these guys dictate most of the feature set and pricing for cloud services.
Gartner also predicts that IT spending on public cloud is going to be up from 208 million dollars which it is was in 2016 up to 5x the amount within 2020. Why shouldn’t they? There can be many advantages of moving to the public cloud for a simple business if they do it right.
* Cost Control
I’m not going to say that moving to cloud is going to save you money, but it is going to be give you a better overview on how much money you are actually using on IT infrastructure and will also make it easier to control the usage since in most cases you only pay for what you use or you have a monthly subscription
* Flecibility
To take advantage of new features which are constantly being developed and added to allow customers, quicker time-to-market with new services and features.
* Scaleability
The ability to scale up and down resources based upon different metrics or schedules, for instance for ecommerence and black friday having that capability is a key essence in cloud
* Security
Of course when I talk about security here (before I go more in-depth) I’m mostly talking about the physical security aspect, since I know from real life experience that some customers have had their small business server standing under their desk or having a small rack in a room where the washing lady also has access. Moving those type of customers to public cloud will gain alot of benefits from the heavily invested cloud datacenters which the different vendors have.
So can we trust the cloud providers with our data? There are new reports about data leakage and hacking happening everyday, so can we trust them with our data? of course many vendors go to great lengths to ensure that they can be trusted with your or your customers data.
All of the providers, stribe after being certified within many different standards, to convince partners that they have routines in place for how they handle physical security, access control and how to manage customer data. Also there are contry specific standard and customer vertical specific certifications within healthcare for instance which is to ensure that the services they provide are compliant with what you can expect with that services.
Now most cloud providers are certified within the common standard which are ISO 27001 and ISO 27017 where the last one is specifically aimed at cloud services. All vendors are good at exposing this information to customers which standards they comply with and a bit more specifics at how they handle data, sub-vendors they are using and where the seperation of responsibility lies between the customer and the provider. For instance you can view Microsoft, Amazon and Googles compliance information here –>
https://azure.microsoft.com/en-us/support/trust-center/
https://cloud.google.com/security/
https://aws.amazon.com/compliance/soc-faqs/
And also within the EU, there are a lot of different compliance needs like EU Privacy Shield and Safe Harbor, but in May 2018 a new standard will be active for companies which deliver services within EMEA, which is GDPR which is going to separate the providers even more in terms on market share. Now I’m not going to describe it in-depth, but GDPR is all about providing more power back to the consumers in terms of demanding the right to be “deleted” and get insight in how a provider handles / uses their data. It also gives consumers the right to get their data exportable to be moved to a new provider. It also has some requirements in terms of security and if there for instance is a data leakage incident at a cloud provider and sensitive data/information gets exposed and it is determined that the cloud provider did not follow the guidelines, the provider can be fined with up to 20 million euros (at the max)
So of course many companies are not adjusted or able to comply with the GDPR and the largest cloud providers are already ramping up in order to comply with the guidelines there, while smaller companies might have more difficulty with being able to comply with the GDPR which might leave them in a position where they cannot sell their services to customers within EMEA.
This will of course create another barrier between the different providers.
1: Risk – Manage the expectations and educate them on what they sign up for
Now one of the most important security risks I see when talking to customers, is not understanding what they actually signed up for when it comes to cloud services. Many have configured services on their own and got infected with ransomware only to discover that the cloud providers don’t actually do automatic backup of virtual machines. And what we also saw with the S3 outtage is that we saw many businesses go down either because they didn’t design (lacking the knowledge) for it or the accepted the risk that a service might go down. Now all of the cloud providers have options to deliver GEO redundant solution IF you design for it.
Also what I also see is that many don’t understand whats included as part of the Service level agreement on individual services. It might be that many companies are actually using the services not as intended and therefore do not fulfill the requirements to get SLA on that service. Then again the SLA will not help you in an outage it only specifies the compensation in credits you will be refunded if something were to happen. You should also be aware that the SLA and feedback is in most cases not automatic, so you will need to follow up with the provider in most cases you get credits back.
2: Find the balance between risk and productivity
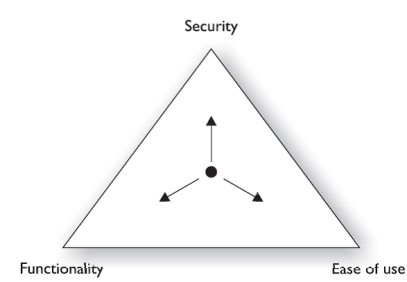
Of course what many IT departments are worried about with cloud is loosing control, from what I’ve seen in many customer examples is where people start using cloud services on their own because the IT department doesn’t want to lose control on where the data is stored. With the upraise of SaaS services using these types of services to empower collaboration between internal employees and external users has become simpler and simpler, so we as IT guys have to empower the users but still having to do a risk assessment and finding the balance between
3: Know your cloud vendor
And of course no cloud provider is identical even though many of them provide services which might be similiar in terms of functions. All of them have different ways to do redundancy, do access control and how data is stored and protected. Another thing is that many providers do so much development that services might be in GA but the documentation team is not up to date and therefore you might not be aware of the full security aspect of that particular service. Of course it might also happen that a cloud vendor uses a service which uses a unsecure API or a service which as a known exploit, but they are often pretty good at notifying customers if these types of incidents occur.
4: Things to think about IaaS – PaaS – SaaS
Stay tuned for part 2…
